Controlling X.509 authentication is essential for IT teams to guarantee secure communication and validate user identities. This involves implementing a strong certificate management policy, utilizing centralized Certificate Authorities (CAs), and employing multi-factor authentication. Key components include managing certificate lifecycles and guaranteeing valid certificates through mechanisms like CRLs and OCSP. IT personnel must be trained on security protocols and remain updated on best practices to prevent unauthorized access. Further exploration reveals more effective strategies for managing X.509 certificates.
Key Takeaways
- Establish a centralized Certificate Authority (CA) to streamline management and enhance control over X.509 certificate issuance and revocation processes. Implement a comprehensive certificate management policy, including regular audits to ensure compliance and security of X.509 certificates. Utilize strong cryptographic algorithms to safeguard against unauthorized access and bolster the security of X.509 authentication. Incorporate multi-factor authentication alongside X.509 to provide an additional layer of security for accessing sensitive systems. Leverage automation and AI tools for real-time monitoring of certificate status and lifecycle management to minimize human error.
Understanding X.509 Authentication
X.509 authentication is a widely adopted standard that defines the format for public key certificates. This standard plays an essential role in establishing a framework for secure communications over networks.
X.509 certificates contain important information, including the public key, the identity of the certificate holder, and the digital signature of a trusted Certificate Authority (CA). These certificates are integral to various protocols, such as SSL/TLS, ensuring that users can authenticate each other and encrypt data.
The hierarchical nature of X.509 allows for a scalable trust model, where CAs can issue certificates to entities, creating a chain of trust. Understanding X.509 authentication is significant for IT teams as they implement security measures to protect sensitive information and maintain integrity in communication.
Benefits of Implementing X.509 Certificates
Implementing X.509 certificates offers numerous advantages for organizations seeking to enhance their security posture.
These certificates provide strong authentication mechanisms, ensuring that only authorized users and devices access sensitive information. By utilizing public key infrastructure (PKI), organizations can facilitate secure communication, protecting data in transit from interception and tampering.
X.509 certificates also support encryption, enabling confidentiality and integrity of communications. Additionally, they reduce the risk of man-in-the-middle attacks, as certificates validate the identities of the communicating parties.
X.509 certificates enhance communication security by ensuring encryption, validating identities, and mitigating man-in-the-middle attack risks.
Moreover, the standardized nature of X.509 facilitates interoperability among various systems and applications, simplifying integration.
Ultimately, adopting X.509 certificates fosters greater trust in digital transactions and enhances overall cybersecurity resilience within the organization.
Key Components of X.509 Authentication
At the core of X.509 authentication are several key components that work in unison to establish secure digital identities.
The X.509 certificate itself is an essential element, encapsulating the public key along with information about the certificate holder and the issuing authority.
Certificate Authorities (CAs) play a significant role by validating identities and signing certificates, ensuring trust in the digital ecosystem.
The certificate revocation list (CRL) and Online Certificate Status Protocol (OCSP) provide mechanisms for checking the validity of certificates, protecting against misuse.
Additionally, the public key infrastructure (PKI) underpins the entire framework, managing the creation, distribution, and revocation of certificates.
Together, these components form a robust system for secure authentication and communication in various IT environments.
Best Practices for Deployment
Effective deployment of X.509 authentication requires adherence to several best practices that guarantee robust security and operational efficiency.
IT teams should ascertain a well-defined certificate management policy, including regular audits of certificate validity and lifecycle management. Utilizing strong cryptographic algorithms is essential to prevent unauthorized access.
Organizations should also implement a centralized Certificate Authority (CA) to streamline management and enhance trust. Regular training for IT personnel on security protocols and potential threats can help mitigate risks.
Additionally, employing multi-factor authentication alongside X.509 certificates can notably enhance overall security.
Finally, establishing a thorough incident response plan enables teams to address potential breaches swiftly, assuring the integrity and availability of authentication services.
Following these guidelines fosters a secure and reliable authentication environment.
Future Trends in X.509 Authentication
As the digital landscape continues to evolve, the future of X.509 authentication is poised for significant advancements. Organizations are expected to adopt innovative approaches to enhance security, efficiency, and interoperability.
Key trends are likely to include:
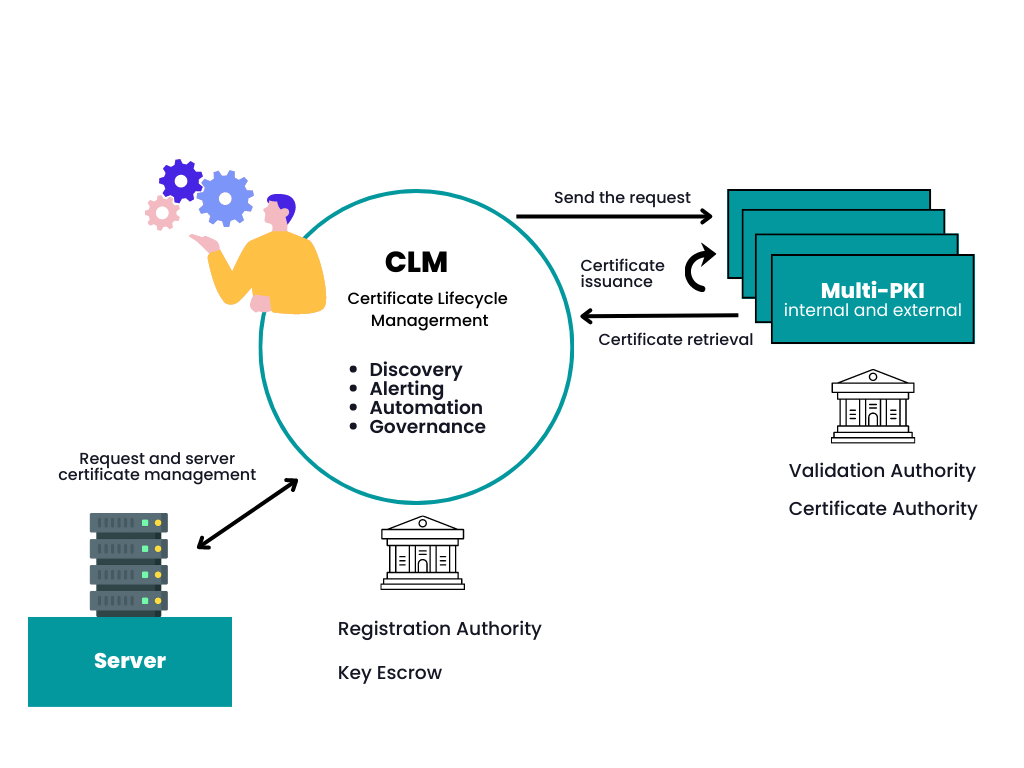
Integration with Blockchain Technology: Utilizing blockchain for decentralized identity management to bolster trust and reduce fraud. Adoption of Quantum-Resistant Algorithms: Preparing for the era of quantum computing by implementing cryptographic algorithms that can withstand quantum attacks. Increased Use of Automation and AI: Leveraging artificial intelligence for real-time monitoring and automated certificate management to minimize human error and streamline processes.
These trends suggest a dynamic future, emphasizing the importance of X.509 authentication in securing digital identities and transactions.
FAQ
How Do X.509 Certificates Impact System Performance?
X.509 certificates play an essential role in establishing secure communications over networks.
Their impact on system performance can vary; while they enhance security through authentication and encryption, the overhead associated with certificate validation and management may introduce latency.
Additionally, larger certificate sizes can lead to increased processing times during handshakes.
As a result, while X.509 certificates provide significant security benefits, they can also impose performance trade-offs that organizations must consider in their system architecture.
What Is the Cost of Implementing X.509 Authentication?
The cost of implementing X.509 authentication can vary considerably based on several factors.
Organizations may incur expenses related to purchasing certificates from trusted Certificate Authorities, setting up necessary infrastructure, and integrating authentication processes into existing systems.
Additional costs may arise from ongoing maintenance and renewal of certificates, as well as training personnel to manage the authentication framework effectively.
Can X.509 Certificates Be Used for Non-It Purposes?
Like a key opening a treasure chest, X.509 certificates can indeed be utilized beyond IT domains.
These digital https://newsmules.com/top-rated-pki-management/ certificates serve various purposes, such as securing email communications, ensuring authenticity in digital signatures, and even enabling secure transactions in e-commerce.
Their versatility allows them to safeguard personal identities and validate documents, making them invaluable tools in a world increasingly reliant on digital interactions.
Therefore, their application extends well beyond the confines of technology.
How Often Should X.509 Certificates Be Renewed?
The renewal frequency of X.509 certificates typically depends on the policies of the issuing authority and the specific requirements of the organization.
Generally, certificates are renewed every one to three years. Regular renewal is essential to maintain security and trust, as expired certificates can lead to vulnerabilities and service disruptions.
Organizations should also consider implementing automated systems to track expiration dates and streamline the renewal process, ensuring uninterrupted service and compliance.
What Happens if a Certificate Is Compromised?
If a certificate is compromised, one might imagine the digital world throwing a grand party to celebrate chaos.
Alas, the reality is grim; trust evaporates faster than a magician's rabbit. The compromised certificate allows unauthorized access, jeopardizing sensitive data and systems.

The fallout can lead to identity theft, financial loss, and reputational damage. Consequently, the once-proud certificate becomes a cautionary tale, reminding all of the importance of vigilance and timely renewal in cybersecurity.
Conclusion
In summary, the adoption of X.509 authentication serves as a sturdy lighthouse guiding IT teams through the complex waters of digital security. By harnessing its benefits and adhering to best practices, organizations can guarantee robust protection against evolving threats. As technology continues to advance, staying informed about future trends will be vital. Ultimately, X.509 authentication stands as a timeless fortress, ready to safeguard sensitive information in an ever-changing digital landscape.